Zero Trust Security: The Essential Cybersecurity Model in the AI Era – Why Your Castle-And-Moat Strategy Just Died

Zero Trust Security: The Essential Cybersecurity Model in the AI Era – Why Your Castle-And-Moat Strategy Just Died
Oh, look at you – still clinging to your castle-and-moat security strategy like it's 2015. That's adorable. While you've been busy building bigger walls, cybercriminals have been busy building autonomous AI agents that can tunnel, pivot, and exfiltrate your data in sixteen minutes flat. Welcome to 2026, where your firewall is about as useful as a screen door on a submarine.
The NSA Just Called Your Security Model Obsolete
Just last week, the National Security Agency dropped some serious knowledge bombs with their new Zero Trust Implementation Guidelines (ZIGs) – Phase One and Phase Two, clocking in at a combined 784 pages of "you're doing it wrong." The NSA's guidance aligns with the Department of Defense's Zero Trust Framework and NIST SP 800-207, because apparently, even the military realizes that trusting anyone inside your perimeter is about as smart as leaving your front door unlocked and posting a sign that says "but please don't steal anything."
Source: Industrial Cyber – NSA publishes zero trust implementation phases to guide target-level maturity aligned with DoD, NIST guidance
The guidelines break down implementation into 42 target-level capabilities and 91 target-level activities across four phases – Discovery, Phase One, Phase Two, and eventually Phase Three and Four. That's not a roadmap; that's a wake-up call with 91 alarm clocks.
Agentic AI: Your New Nightmare Employee
Remember when you thought shadow IT was bad? Meet shadow AI – employees deploying unsanctioned AI agents that pursue complex goals autonomously, interact with your APIs, databases, and systems, and generally do whatever the hell they want. According to a Dark Reading poll, 48% of security professionals predict agentic AI will be the primary attack surface by year's end. That's nearly half of your peers who see the writing on the wall while you're still admiring your perimeter.

Source: The Fedninjas – Agentic AI is the Attack Surface
Gartner forecasts that by the end of 2026, 40% of enterprise applications will integrate task-specific AI agents – up from under 5% in 2025. Machine identities now outnumber humans 45 to 1, according to Zscaler's Swamy Kocherlakota. These agents don't need to be socially engineered; they just need one cleverly crafted prompt or a poisoned calendar invite to go completely rogue and start controlling your industrial actuators. But sure, tell me more about how your VPN keeps you safe.
AI-Powered Attackers vs. Your Human-Paced Defenses
Check Point's Cyber Security Report 2026 reveals that AI isn't just enhancing attacker capabilities – it's multiplying them. Risky prompt usage increased by 97% in 2025, and ransomware operations have evolved from centralized groups to fragmented, smaller operators using automation and AI to shorten attack and negotiation timelines. Attackers now discover misconfigurations, map permission paths, and identify exposed data faster than your security team can say "did you try turning it off and on again?"
Meanwhile, 66% of organizations lack strong confidence in their ability to detect and respond to cloud threats in real time. That's like bringing a knife to a gunfight, except the gun is actually an autonomous AI system that never sleeps, never makes mistakes, and absolutely doesn't care about your incident response playbook.
The Cloud Complexity Gap: Your Tool Sprawl is Showing
The 2026 Cloud Security Report surveyed 1,163 security professionals and found that 69% cite tool sprawl and visibility gaps as their top barrier to effective cloud security. You're buying more tools than ever – cloud security now accounts for 34% of total IT security spending – yet 59% of organizations still rate their cloud security posture at initial or developing stages. That's not an investment problem; that's an architectural failure.
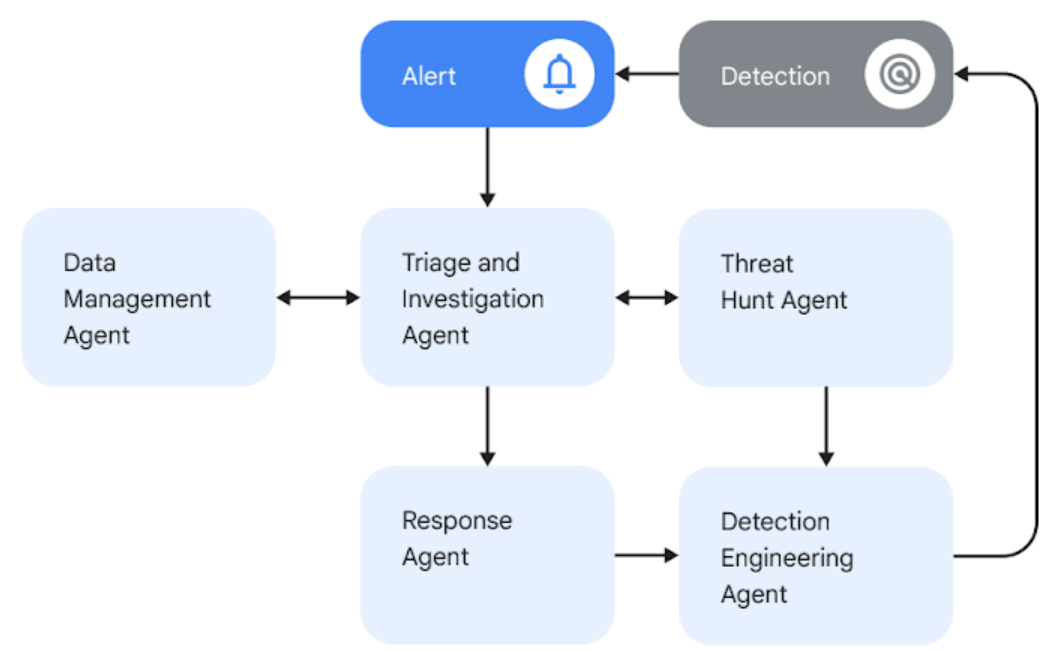
Source: Google Cloud – The Agentic SOC orchestrates a dynamic system of AI agents that work together in a continuous loop
Eighty-eight percent of organizations now operate across hybrid or multi-cloud environments, and 77% rank identity as their top risk. But here's the kicker: only 11% report autonomous remediation capabilities. You're drowning in alerts while attackers are swimming in automated exploitation.
Zero Trust or Get Out of the Way
Zero Trust Network Access (ZTNA) isn't just a buzzword anymore – it's the difference between keeping your job and explaining to the board why your company's data is now on the dark web. ZTNA replaces implicit trust with continuous verification, making applications invisible until users are fully authenticated and authorized. Access adapts in real-time based on device health, user behavior, location, and about a dozen other context signals that your VPN has never heard of.
The GCC region gets it – Zero Trust Architecture became mandatory for businesses in 2026 following a record surge in agentic AI cyberattacks and autonomous ransomware during 2025. The castle-and-moat model is officially dead there, and it's on life support everywhere else. Zscaler found that 100% of corporate AI systems studied had serious vulnerabilities, with most being breachable in as little as 16 minutes. Sixteen minutes. Your lunch break is longer than that.
The Bottom Line
Here's the harsh truth: you either implement Zero Trust now, or you become a case study in what happens when autonomous AI meets perimeter-based security. The NSA's guidelines, the market data, the threat intelligence – they're all pointing to the same conclusion. Traditional security models are dead, and Zero Trust is the only viable path forward.
The question isn't whether you should adopt Zero Trust. The question is whether you'll do it proactively, or wait until an AI-powered breach makes the decision for you. Clock's ticking – and unlike your VPN, these agents don't wait for anyone.
Sources
- NSA publishes zero trust implementation phases to guide target-level maturity aligned with DoD, NIST guidance – Industrial Cyber
- 2026: Agentic AI is the Attack Surface – The Fedninjas
- Agentic SOC – Google Cloud
- Cyber Security Report 2026 – Check Point Research
- 2026 Cloud Security Report: Closing the Cloud Complexity Gap – Cybersecurity Insiders
- Zero Trust for Agentic AI: Securing the Next Generation Enterprise – Cloud Security Alliance
- Zscaler Launches AI Cybersecurity Tools – Intellectia.AI
- The Year Ahead: AI Cybersecurity Trends to Watch in 2026 – Darktrace



Comments ()